Overview
Visitor Single Sign-On (SSO) feature allows you to authenticate your visitor’s account information before the chat starts.
Once customers log in, your agents can view their account information in Comm100 Live Chat. This helps them know who they are chatting with and avoid asking the same standard questions, speeding up the resolution, and improving customer satisfaction.
How Visitor SSO works?
Comm100 Live Chat Visitor SSO uses SAML (Security Assertion Mark-up Language), an XML based open-standard data format for exchanging authentication and authorization data between your IDP (Identity Provider) and the Comm100 Live Chat server.
When a customer clicks on the login option in the chat window, the Comm100 Live Chat server asks your IDP server whether the customer has been authenticated. If the customer has already logged in SSO using the same browser, the IDP server returns the response to Comm100, and the customer is connected to live chat immediately, otherwise, the login page shows up in the chat window, asking customers to log in.
The credentials provided in the page are sent directly to your SSO server, not Comm100, which means this process of authenticating is done solely on the SSO service side, preventing man-in-the-middle hacks and other possible password breaches. Once authenticated, customer account information is sent to Comm100 Live Chat.
Your agents can see the information right in the Agent Console where you chat with customers. You can also make SSO authentication optional. Customers who choose to chat as a visitor skips the authentication step. In this case, your agents cannot view their account information in Comm100 Live Chat.
Requirements for Setting up Visitor SSO
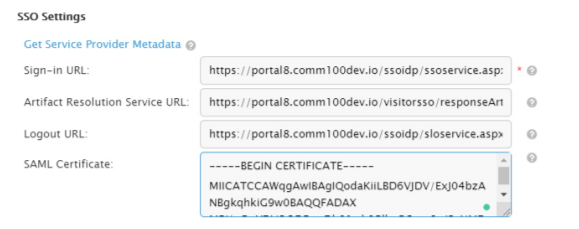
Before configuring Visitor SSO, collect the following details:
- The SSO Sign-In URL which can receive SAML Request
- Artifact Resolution Service URL
- Logout URL
- SAML Certificate.
To ensure data security, Comm100 suggests adding a signature to the SAML Response returned from IDP to Comm100 SSO, which requires a certificate to verify signature validation.
Note: Collect the service provider metadata from Comm100 and share the file with your identity provider. The Sign-in URL, Artifact Resolution Service URL, Logout URL, and the SAML Certificate is provided by your IDP.
Enabling Visitor SSO in Your Comm100 account
After gathering the information, follow these steps:
- Log in to your Comm100 account.
- Go to the Live Chat tab.
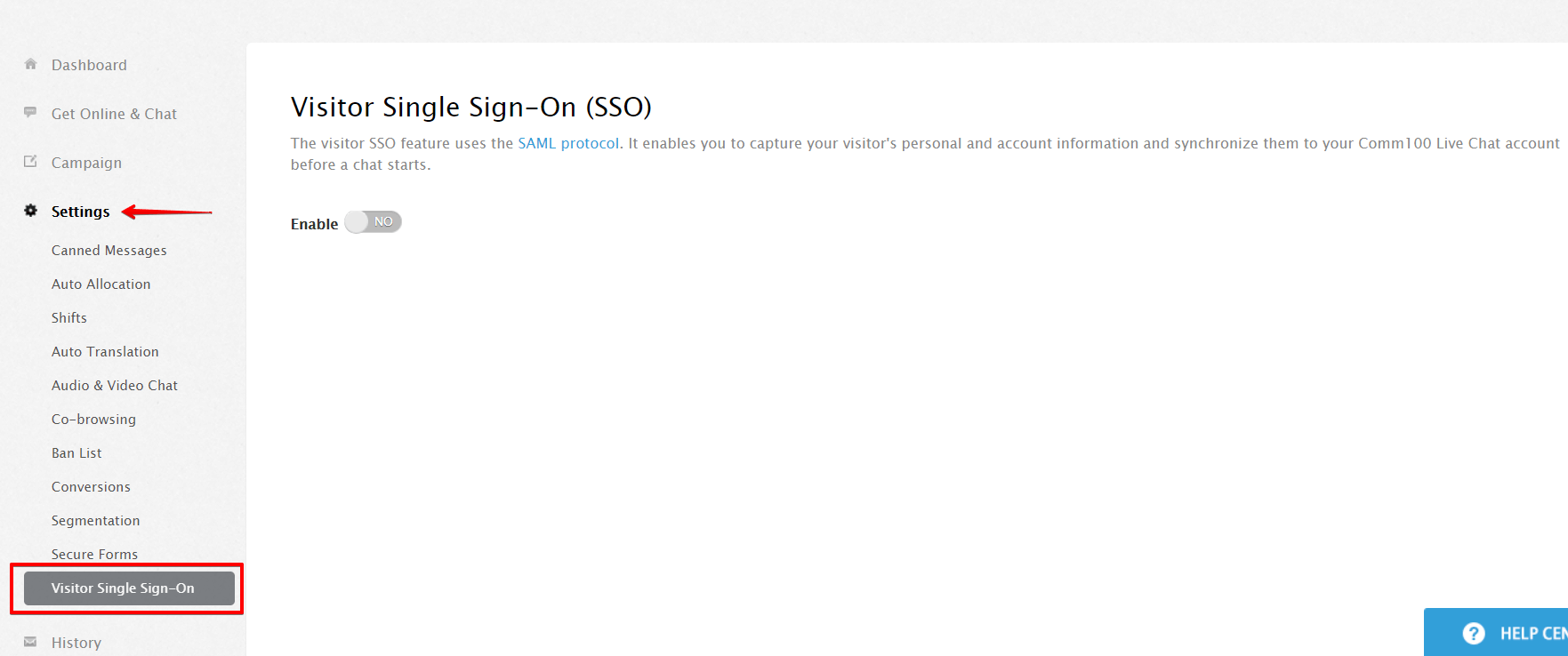
- From the left menu, click Settings, and go to Visitor Single Sign-On.
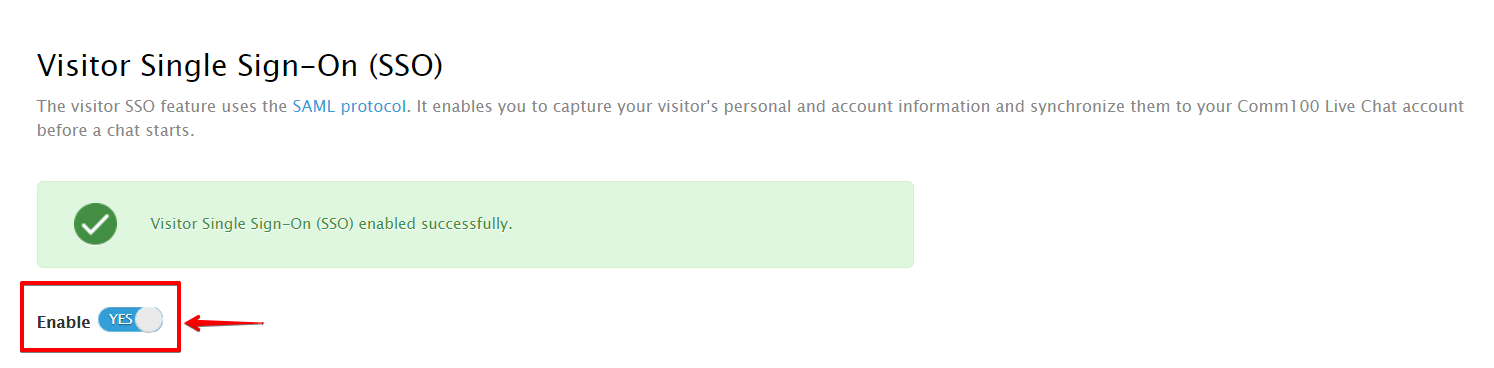
- On the Visitor Single Sign-On page, turn ON the Enable toggle key.
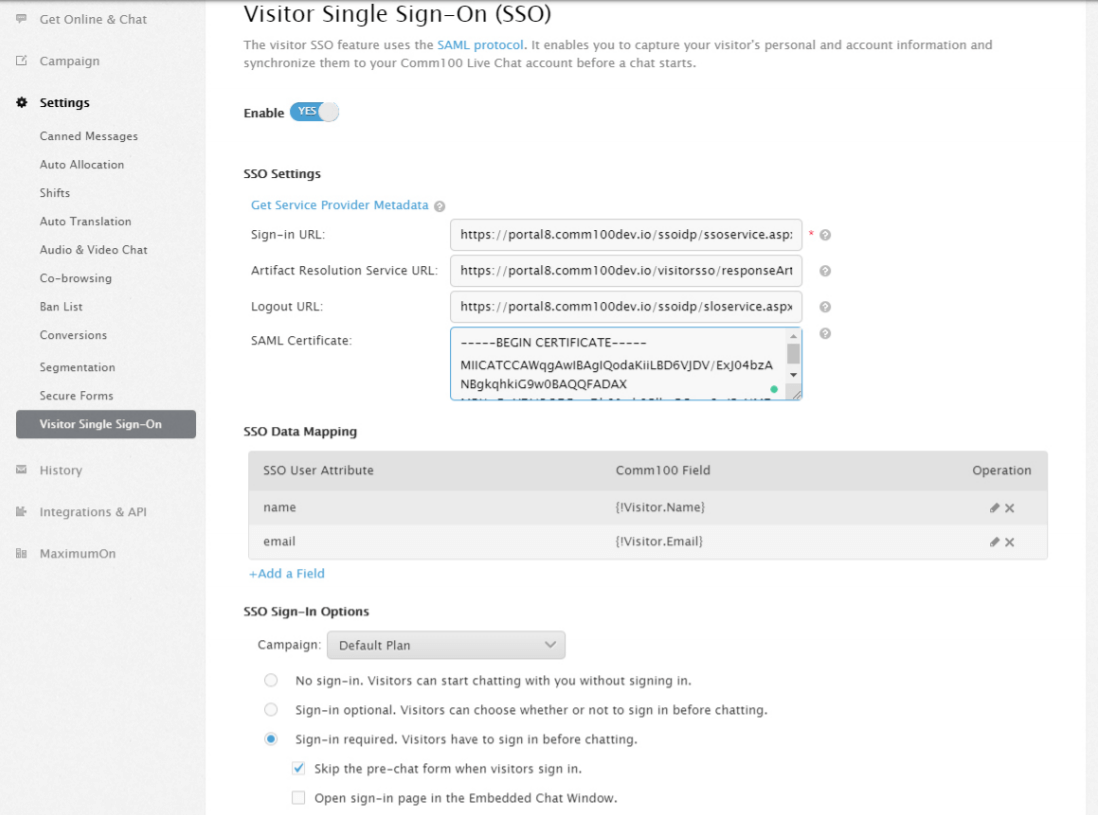
- In the SSO Settings section, add all information that you have gathered.
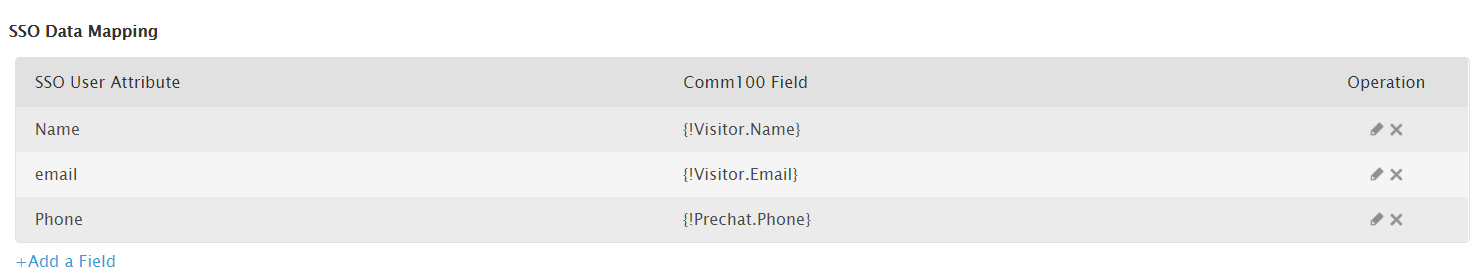
- In the SSO Data Mapping section, add all user attributes that you wish to collect.
You can collect visitor information, like name, email, and phone number, and so forth. - Define the sign-in requirements in the SSO Sign-In options.
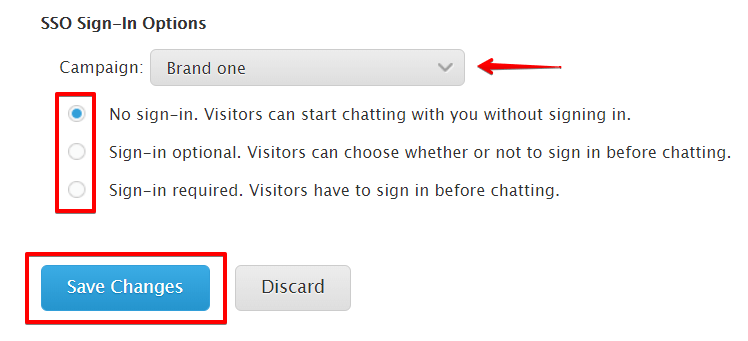
From the Campaign drop-down list, select the campaign and define whether your customers need to sign into their accounts with you before chatting.
Three sign-in options are available to satisfy different business requirements:
- No Sign-In: Your customers and visitors can start chatting with you right after clicking on your chat button, or after filling out your pre-chat survey (if you have pre-chat survey enabled).
- Sign-In Optional: Give your customers and visitors the choice to log into their accounts or chat anonymously when initiating a chat. Logged-in customers will skip the pre-chat survey, while non-logged in visitors need to fill out your pre-chat survey before chatting.
- Sign-In Required: Your customers and visitors are required to log in prior to chatting. If a visitor does not have an account with you, he/she will not be able to access live chat. This option helps you automatically keep out ineligible visitors if your live chat is exclusive to customers with accounts.
- Click Save Changes.
To learn more about Visitor SSO, click here to read the Visitor Single Sign-On Whitepaper.